Agile Development
Responsive UI/UX Design
Professional SEO Services
Custom Made System
Empowering Innovation Through AI
PHILOSOPHY
Not invention, it is VALUE innovation
About US
Grid Technology was founded in 1996. We are the leading innovator of tailor-made systems and solutions in Asia. Our slogan, "VALUE innovation" is the cornerstone of BLUE OCEAN STRATEGY, which helps our client businesses achieving in both sustainability and a positive impact on profitability.
In this era of advanced technology, AI plays a crucial role in shaping our future. We're excited to be part of the journey towards making life better for everyone. Our unwavering dedication is focused on using AI to create positive impacts in people's lives.
What is our focus?
- We offer consultation services to enhance your business.
- We create profitable business models that drive value innovation.
- We leverage IT to develop tailored systems for your organization.
- We ensure your competitive edge in new markets.
- Web application development, especially in financial related aspect
- Domain and DNS management
- Email server management including SPF and DKIM
- AI Chatbot (GPT-4 / GPT-4o Omni)
AI Partners (ChatGPT-4/4o Omni)
Leveraging AI is undoubtedly important, but the critical thinking lies in how we adapt to and coexist with it in order to optimize productivity. The key is finding the right balance and integration of human and artificial intelligence to enhance our capabilities, rather than viewing AI as a replacement or threat.
Portfolio
Take a moment to explore some of our recent projects. While most of the sites below were created by us from scratch, we engage in various ways with our clients' websites. Our services include web design, development, consulting, maintenance, graphics, marketing, and much more!

The Incorporated Owners of Gold Ning & Gold King Mansions
Embed Google Drive API to archive effective document management system.

CSC Loan
CSCLoan provides instant cash for you. It comes with a smart prepayment calculator. The transaparent informaiton enables you to have a good planning for your future businesses.

beyond.com.hk HK Community
2025年6月30日,beyond.com.hk 官方網站終於上線了!這對全世界的粉絲來說絕對是個好消息!網站提供多種娛樂功能和豐富資訊,包括新聞剪報翻頁書、歷史影片剪輯、多位作家的作品以及精彩的音訊內容。成為會員或付費訂閱用戶後,您將能夠解鎖所有娛樂功能。
TESTIMONY
For businesses of all sizes, success relies significantly on word of mouth. We are grateful for the positive feedback we've received.
Thank you for your encouragement and support!

"Thanks to Grid Technology for developing the systems. It indeed has enabled our business to run like a well-oiled machine while making it more streamlined, more productive, and ultimately, more profitable."
Mr. Casey Leung
CEO – Protech Computer Ltd

"When a huge portion of your business is running smoothly and with less supervision, you can step back and let the systems do the work for you, thereby making you a smarter business owner. Thank you Grid Technology for building these sophisticated systems for us."
Mr. Ben Chong
Business Director – Vertex System Ltd

“Ever thought about getting things done faster? Eliminating bottlenecks? Reducing your workload? Taking a month-long vacation? Working in a different country? Hiring more people? Scaling your business to multiple 7-figures? Thanks to Grid Technology. Your systems allow us to do all these things and more."
Mr. Philip Ng
Pdt. Dev. Manager – Mainfocus Electronic Ltd

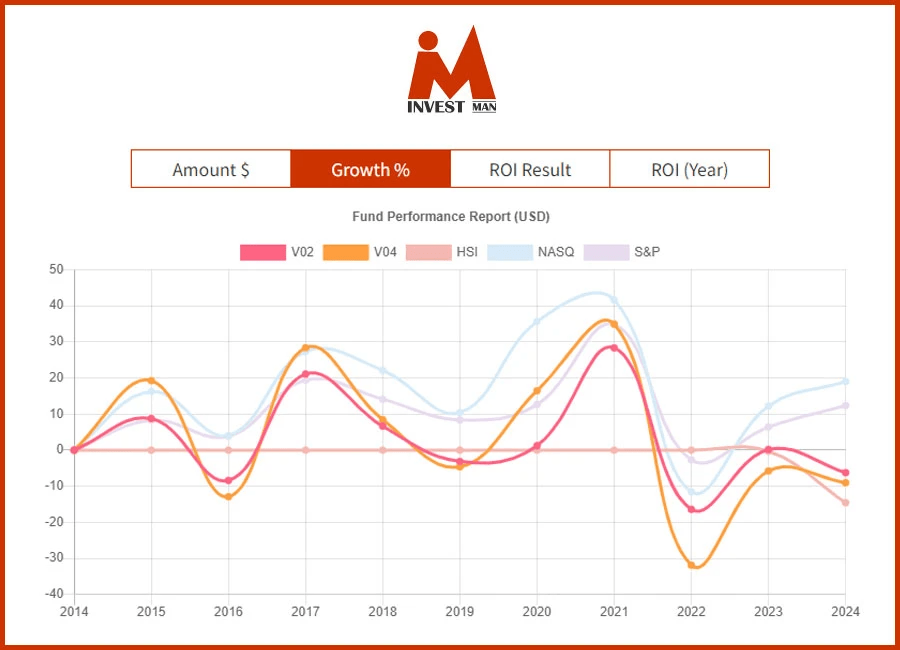
“Thank you, Grid Technology, for building our effective ETF system. Your expertise in research, portfolio construction, data crawling, trend analysis, and data presentation has been invaluable. We highly recommend Grid Technology for its exceptional skills in developing advanced ETF or related financial systems. Thank you for your outstanding service and partnership."
Mr. Desmond Lai
Founder – ETF Connect

“Returning to Toronto presents challenges, but I am grateful to Grid Technology for creating a web application that has been instrumental in expanding and significantly growing my business. I deeply appreciate their passion and dedication."
Mr. James Ngan
Main Chef – Yummy-Yummy Fastfood

“Thanks to Grid Technology for developing an effective fund management system. We no need to struggle with the data. We love the simulator module very much, it's awesome and undefeatable."
Mr. Oscar So
Senior Unit Manager – AIA PMDHK
“Thanks to Grid Technology for delivering the systems that meet our business needs. The systems as a set of processes, tools, people, and strategies that all work together to solve our operational problems and achieve our business goals."
Mr. Tommie Lee
CEO – Beautideal Company Ltd
“感謝 GRID TECHNOLOGY 公司開發了線上即時貸款系統。這個系統增強了客戶的體驗,提供了一個透明及具體的還款計劃。它大大加快審批的流程並降低成本,促進了我們企業的發展。"
Mr. Anthony Chan
Sales Director – CSC Loan
Our Team
Professional Qualification

Eric (MBA/BSc) - Founder
- Master of Business Administration
- NFQ L7 of Strategic Business of IT
- Bachelor of Science in Computer Science
I consider myself a driven and ambitious individual, but deep down, I'm just like anyone else. What truly inspires me is leveraging technology to enhance people's lives through smart integration and process re-engineering. My goal is to create solutions that are not only repeatable and scalable but also unique in their approach, making them stand out and deliver a remarkable value proposition. I strive to make things simpler, more efficient, and ultimately more enjoyable for everyone involved.
"People should not be unfamiliar with strategy, those who understand it will survive, those who do not understand it will perish (Sun Tzu, Art of War)".

Chris (BSc/PMP) - Project Manager
- Bachelor of Science in Computer Science
- Project Management Professional
My passion lies in business transformation, particularly in the ability to streamline processes and operations to generate significant value for clients. The ultimate source of motivation for me is the gratifying moment when clients express their genuine satisfaction, acknowledging the impact of my efforts with words like "Wow, this is really nice. Good work!" These affirmations serve as a testament to the successful delivery of exceptional results and further fuel my drive for excellence.

Ricky (BSc) - Web Specialist
- Bachelor of Science in Web Programming
- Microsoft certified MVC
With a deep passion for new technologies, I have dedicated a significant amount of my professional career to web development, constantly seeking out the latest advancements and trends in the field. I have gained extensive experience and expertise in various aspects of web development, including front-end and back-end technologies, user experience design, and responsive web design. I honed my skills in workflow process development. I have been actively involved in implementing efficient workflow management methodologies and tools to ensure seamless collaboration.

Joey (BAcc) - Financial Manager
- Bachelor of Accounting
Efficiency innovations arise in industries that already exist. They provide existing goods and services at much lower costs. They are not empowering. Efficiency innovators become the low cost providers within an existing framework.

Charles (BFA) - Digital Director
- Bachelor of Computer Engineering
I utilize cutting-edge technologies like AI, virtual production, and XR. Our achievements include contributing to XR TVC production in Shanghai (2022) and producing Hong Kong's first XR TV series (2023). Leading a skilled design team, we aim to pioneer the fusion of art and technology.

Wen (BEng) - Technical Lead
- Bachelor of Computer Engineering
I have over 10 years of IT Consulting and Delivery experience, I possess extensive technical expertise in digital transformation across various industries. I have a solid understanding of MarTech technology stacks including Azure, AWS, Sitecore, Salesforce, and custom solutions.
Let's chill
Contact Us
Office: Room A, 5/F, Everwin Ctr, 72 Hung To Rd, Kwun Tong
Strategic: West Wing 2/F, 822 Lai Chi Kok Rd, Cheung Sha Wan(852) 9161 1116Know Your Threats
Security Consideration
Popular security issues:
Phishing email:
This is a form for you to pretend anyone for sending email. We called it a phishing email! A phishing email is a type of fraudulent email that is designed to deceive recipients and trick them into revealing sensitive information, such as login credentials, financial details, or personal information. Phishing emails are typically disguised as legitimate messages from well-known organizations, such as banks, social media platforms, or online services.
Social Engineering Attacks:
Social engineering involves manipulating individuals to divulge sensitive information or perform actions that compromise security. Educate employees about common social engineering techniques and implement policies to verify requests for sensitive information or actions.
Traditional security issues:
Unauthorized Access:
Protecting against unauthorized access is crucial. Implement strong authentication mechanisms, such as multi-factor authentication, to ensure only authorized individuals can access systems and sensitive data.
Data Breaches:
Data breaches can result in the loss or theft of sensitive information. Implement robust security measures to protect data at rest and in transit, including encryption, access controls, and regular security audits.
Internal organizational threats:
Lack of Security Awareness and Training:
Human error is a common cause of security breaches. Regularly train employees on security best practices, including safe browsing habits, password hygiene, and how to identify and report security incidents.
Weak Passwords:
Weak passwords pose a significant security risk. Enforce password complexity requirements, encourage the use of password managers, and consider implementing passwordless authentication methods.
Malware and Ransomware:
Malicious software, including ransomware, can cause significant damage to systems and data. Implement robust antivirus and anti-malware solutions, regularly update software, and educate users about safe browsing habits and email practices.
Insider Threats:
Insider threats refer to malicious activities by employees or contractors with authorized access to systems and data. Implement security controls, user access management, and regular monitoring to detect and prevent insider threats.
Insecure APIs:
Application Programming Interfaces (APIs) are commonly used to connect different systems and applications. Ensure APIs are properly secured, using authentication, access controls, and encryption to protect against API-related vulnerabilities.